Two-Day Cybersecurity Workshop
Target Audience and attended
- Undergraduate and postgraduate engineering students (CSE, IT, ECE, AIML, and related streams)
- Beginner to intermediate level (no prior deep security knowledge assumed, but technical aptitude required)
Objectives of This Workshop
- Understand fundamental cybersecurity concepts
- Recognize common cyber threats
- Learn preventive measures
- Apply best practices for personal and organizational safety
- Gain awareness of tools used in cybersecurity
Why Cybersecurity Matters
- Almost every task—from studying and banking to communication and shopping—depends on the internet. This constant connectivity exposes users to cyber threats. Effective cybersecurity helps:
- – Protect confidential and financial data
- – Prevent misuse of personal identity
- – Secure online interactions and transactions
- – Maintain trustworthy digital environments
- – Reduce the risk of cybercrime
Major Cyber Threats to Be Aware Of
- Malware: Software created to harm devices or steal information. Examples include spyware, ransomware, and trojans.
- Phishing Attacks: Messages designed to trick users into sharing sensitive information by pretending to be legitimate organizations.
- Social Engineering: Techniques used by attackers to manipulate people into revealing private data, often by exploiting emotions like fear or urgency.
- Password-based Attacks: Attempts to guess or steal passwords through brute-force tools, leaked credentials, or malicious programs.
- Network Threats: Cybercriminals may intercept or disrupt networks through attacks such as MITM (Man-in-the-Middle) or DDoS.
- Insider Risks: Threats arising from employees or trusted individuals—either by mistake or intentionally
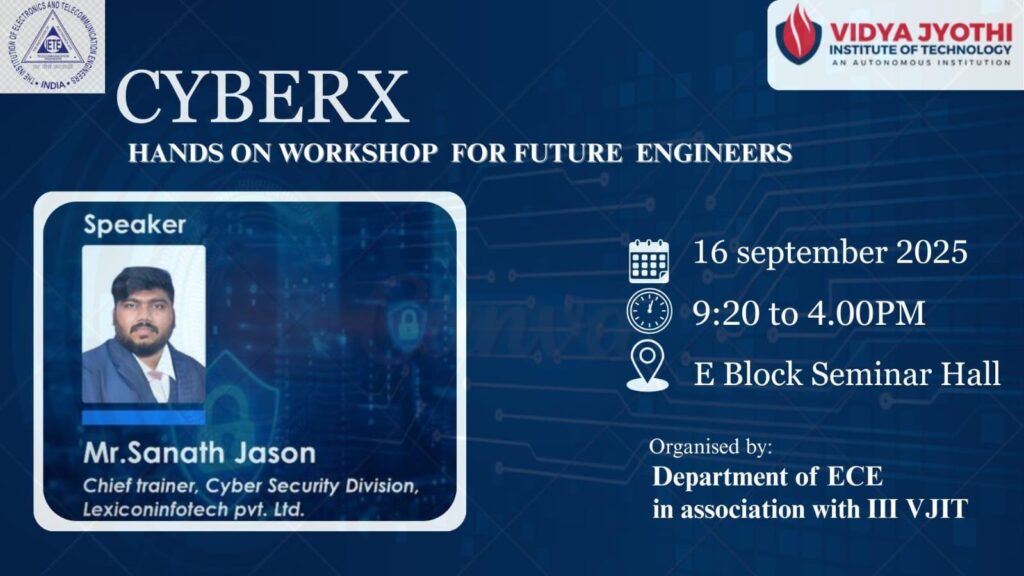
Duration & Schedule DAY-1
Date & Venue: VJIT HYDERABAD,
Total Duration: 7–8 hours (single-day intensive, workshop + live hands-on).
Agenda
Session 1: Introduction to Cybersecurity Landscape (9:30 AM – 10:30 AM)
- Global & Indian cyber threat scenarios
- Real-world case studies: Aadhaar leaks, ransomware in Indian hospitals, WannaCry, Pegasus spyware
- Cybersecurity career pathways (Ethical Hacking, Red Teaming, Blue Teaming, Forensics, IoT/Cloud Sec)
Session 2: Fundamentals of Ethical Hacking & Attack Vectors (10:30 AM – 12:00 PM)
- How hackers think: attacker mindset
- Stages of hacking: Reconnaissance → Scanning → Exploitation → Post-Exploitation
- Lab Demo 1: Footprinting and scanning using Nmap, Shodan, Maltego
- Hands-On Task: Students scan a test lab machine to identify open ports & vulnerabilities
Tea Break (12:00 PM – 12:15 PM)
Session 3: Web & Application Security – Live Hacking (12:15 PM – 1:30 PM)
- OWASP Top 10 vulnerabilities
- SQL Injection, XSS, CSRF explained with real-time examples
- Lab Demo 2: Exploiting a vulnerable demo site (e.g., DVWA / Juice Shop)
- Hands-On Task: Students try SQL error-based injection & XSS in safe lab setup
Lunch Break (1:30 PM – 2:15 PM)
Session 4: Wireless & Network Security Challenges (2:15 PM – 3:30 PM)
- Wi-Fi hacking basics – WPA2/WPA3 cracks, network sniffing
- Lab Demo 3: MitM attack using Ettercap or Wireshark packet capture
- Hands-On Task: Capture network packets & detect plain-text credentials
DAY-2

Session 5: Incident Response and Digital Forensics (9:30 AM – 11:30 PM)
- How cyber forensics works in government investigations
- Basics of log analysis and tracing attackers
- Lab Demo 4: Memory dump analysis (Volatility framework intro)
- Hands-On Task: Students find suspicious activity in given log files
Tea Break (4:30 PM – 4:45 PM)
Session 6: Capture The Flag (CTF) Cybersecurity Challenge (11:45 PM – 1:00 PM)
- Teams of students compete in a mini-CTF event
- Challenges: Simple hacking tasks on web apps, steganography, password cracking, network forensics
- Incentives: Top teams get certificates of excellence + cybersecurity book / merchandise
Closing Session & Career Guidance (2:00 PM – 3:00 PM)
- Recap of the day’s learnings
- Certification distribution
- Career roadmap: How to start in cybersecurity, resources, certifications (CEH, OSCP, CHFI, CISSP, etc.)
Key Features of the Workshop
- 80% practical, 20% theory
- Real-world case studies tied to Indian ecosystem
- Live hacking demos & controlled lab environment
- Mini CTF to build student enthusiasm
- Certificates for all participants, special awards for winners
- Access to workshop material, cheat sheets, and free tools
Technical Requirements
- Linux VM, Kali Linux, vulnerable apps pre-installed
- Projector + sound system for live demos
- Isolated Wi-Fi or test network for ethical exercises
- Pre-installed tools on participant laptops (VMware, Kali ISO, DVWA, Wireshark, Burp Suite Community, etc.)
Pricing (Student-Friendly Model)
- Individual Registration: ₹1249 per student (includes workshop, tools, material, snacks, certificate)
- Group Discounts: ₹1099 per student for groups of 5+
- Institution Sponsorship: Colleges can do bulk registration at ₹95,000 for up to 100 students (easy for departments)
Value-Add Opportunities
- Best students from the attendees ,3 studentswere offered internship opportunities in cybersecurity labs
- Networking with industry professionals invited as guest speakers
- Follow-up online Q&A support for 1 month











0 Comments